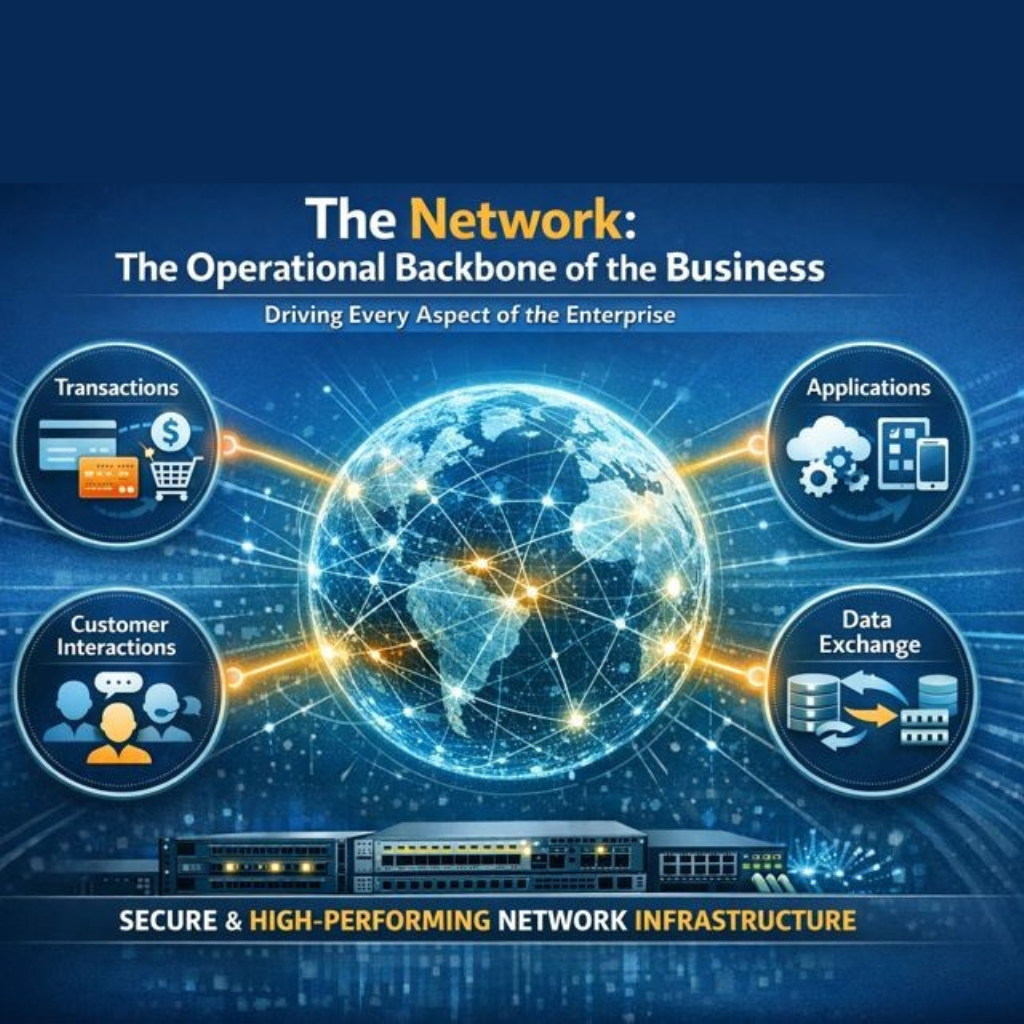
For today’s enterprises, the network is far more than an IT asset. It is the operational backbone of the business. Every transaction, application, customer interaction, and data exchange depends on a secure, high-performing network infrastructure. Gartner’s 2025 research highlights this reality, with 89% of organizations identifying network availability and reliability as critical to business continuity. At the same time, growing adoption of cloud services, distributed architectures, and remote work has expanded the attack surface. Cisco’s 2024 Annual Cybersecurity Report notes that 71% of breaches now involve vulnerabilities in complex, interconnected network systems, underscoring how the expansion of network environments introduces new risks.
From phishing and social engineering to ransomware and lateral movement attacks, cyber threats evolve faster than most organizations can respond. The uncomfortable truth is that most breaches do not occur because security tools are absent, but because weaknesses within the network weaknesses go undetected for too long. This is why routine network security testing must be treated as a core element of enterprise risk management. It is not a one-time compliance exercise, but an ongoing, strategic discipline.
The Role of a Resilient Network in Business Continuity
A resilient network does more than enable connectivity. It protects sensitive data, sustains critical operations, and preservers trust with customers and stakeholders. A single overlooked issue, such as an unpatched firewall rule, misconfigured VPN, or an exposed endpoint, can quickly escalate into wide-reaching disruption.
For business and IT leaders, the question is no longer whether network security should be tested, but how consistently and intelligently it is done. Routine network shifts from a reactive function to a proactive, measurable practice that strengthens both technical defenses and organizational confidence.
The Structural Challenges Leaders Rarely See
1️⃣ Data Abundance Without Decision Clarity
Networks now generate unprecedented volumes of telemetry. Yet more data has not translated into better decisions.
Instead, leaders face:
- Alert fatigue that hides real issues
- Signals without context or business impact.
- Problems detected late after incidents, not prevented early
When insight arrives late, the business absorbs the impact.
2️⃣ Complexity as the New Normal
Enterprise networks are no longer contained environments. They span hybrid clouds, edge locations, mobile workforces, and connected devices. Each layer adds operational interdependence—and risk.
Complexity itself is not the problem. Unmanaged complexity is. When visibility is fragmented, accountability diffuses, and resilience weakens.
3️⃣ Legacy Systems as Silent Risk Carriers
Many organizations still rely on infrastructure designed for a simpler era. These systems were not built for real-time analytics, modern security threats, or continuous compliance.
Legacy environments often:
- Obscure critical network behavior
- Slow down root-cause analysis
- Expand the attack surface without detection
They remain in place not because they are safe—but because replacing them feels disruptive. The risk they introduce is rarely visible until it is too late.

 The False Economy of Under investment
The False Economy of Under investment
Monitoring is often evaluated as a cost line item rather than a risk-mitigation lever. As a result, modernization is deferred and coverage remains incomplete.
The outcome is predictable:
- Lower upfront spend
- Higher exposure to outages
- Significantly higher costs when failure occurs
Resilience is expensive only when it is absent.
5️⃣ Growth Without Scalable Visibility
As enterprises scale, their networks expand faster than their monitoring frameworks. New users, applications, and services increase operational load—but monitoring often remains static.
When visibility fails to scale, risk compounds silently. What appears to be progress becomes fragile.
6️⃣ Compliance as an Operational Constraint
Monitoring tools process sensitive business and customer data. Regulations such as GDPR, PCI DSS, HIPAA, and RBI mandates impose strict expectations around data governance.
When monitoring architectures are not compliance-aligned by design, organizations inherit legal, financial, and reputational exposure.
 The Talent Gap No Tool Can Solve Alone
The Talent Gap No Tool Can Solve Alone
Even the most advanced platforms depend on skilled professionals to interpret signals and act decisively. That expertise is increasingly scarce.
Without sufficient expertise:
- Alerts go unresolved
- Configurations drift
- Risk accumulates quietly
Technology without talent is a false sense of security.
 A Threat Landscape That Refuses to Stand Still
A Threat Landscape That Refuses to Stand Still
Networks evolve daily. Threats evolve hourly. Static monitoring strategies age quickly. Modern resilience requires systems that adapt, learn, and respond in real time—without waiting for human intervention.
Reframing Network Monitoring as a Strategic Capability
The most resilient enterprises no longer treat network monitoring as an operational task. They treat it as a business capability—one that protects revenue, trust, and continuity.
Increasingly, leaders recognize that managing this complexity internally is inefficient and risky. Strategic partnerships with managed service providers offer:
- Continuous, proactive monitoring
- Advanced analytics and automation
- Built-in compliance controls
- Expertise across legacy and modern environments
This model shifts organizations from reactive firefighting to predictive control.
What Resilient Organizations Do Differently
Enterprises that modernize their monitoring strategy consistently achieve:
- Fewer high-impact outages
- Faster incident resolution
- Stronger security posture
- Lower operational risk
- Greater confidence in scaling digital initiatives
They do not eliminate complexity—they master it.
The Leadership Question That Matters
Hidden network challenges are not technical failures. They are leadership blind spots.
The enterprises that succeed in the next phase of digital growth will be those that recognize network monitoring not as a toolset, but as a strategic enabler of resilience, trust, and competitive advantage.
The network is no longer just infrastructure. It is business continuity.
If your network underpins your strategy, your monitoring strategy should reflect that reality. Talk to us today.
